Add repository secret
In your repo: Settings → Secrets and variables → Actions → New repository secret.Name:
GARNET_API_TOKEN · Value: your token from app.garnet.ai → Settings → API Tokens.Verify
Push or open a PR. Run appears at app.garnet.ai within seconds.
Configuration
| Parameter | Description | Required | Default |
|---|---|---|---|
api_token | Garnet API token | Yes | — |
debug | Verbose workflow logs | No | false |
Job Summary
Garnet writes a Runtime Report to the Job Summary automatically.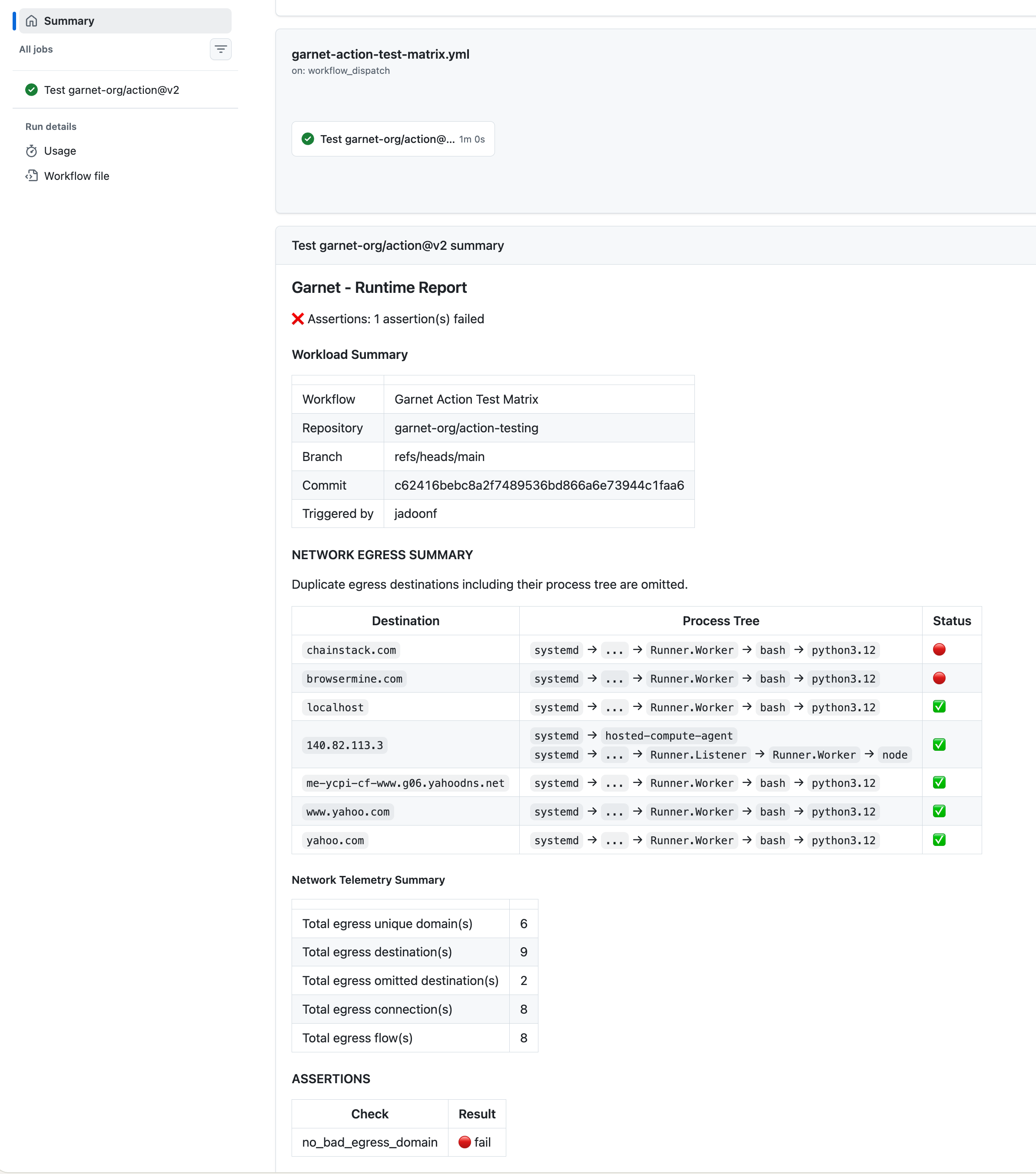
Why sudo
Jibril attaches eBPF at the kernel level — requires sudo during install.ubuntu-latest includes it by default. See Architecture for the safety model.
Troubleshooting
Agent doesn't appear in the dashboard
Agent doesn't appear in the dashboard
Verify
GARNET_API_TOKEN is set. Check workflow logs for the Garnet step.Permission denied
Permission denied
Requires sudo for eBPF.
ubuntu-latest includes it by default.No Job Summary
No Job Summary
Use the pinned v2 SHA:
garnet-org/action@f4a67ff8e102a293fcf5f9fdfb34656717d2f45e.Debug mode
Debug mode