See what your code actually does when it runs. Garnet adds kernel-level telemetry — network, process, file — directly to your CI review flows, catching unexpected behavior and supply chain risk before merge.Documentation Index
Fetch the complete documentation index at: https://docs.garnet.ai/llms.txt
Use this file to discover all available pages before exploring further.
Quick start
Token → sensor → first run in minutes.
Architecture
Deploy → monitor → assert, and eBPF safety.
Runs
Kernel-level profile of each execution with check results.
Checks
Runtime checks — like unit tests for what code actually does.
Agents
Jibril eBPF sensors on runners and hosts.
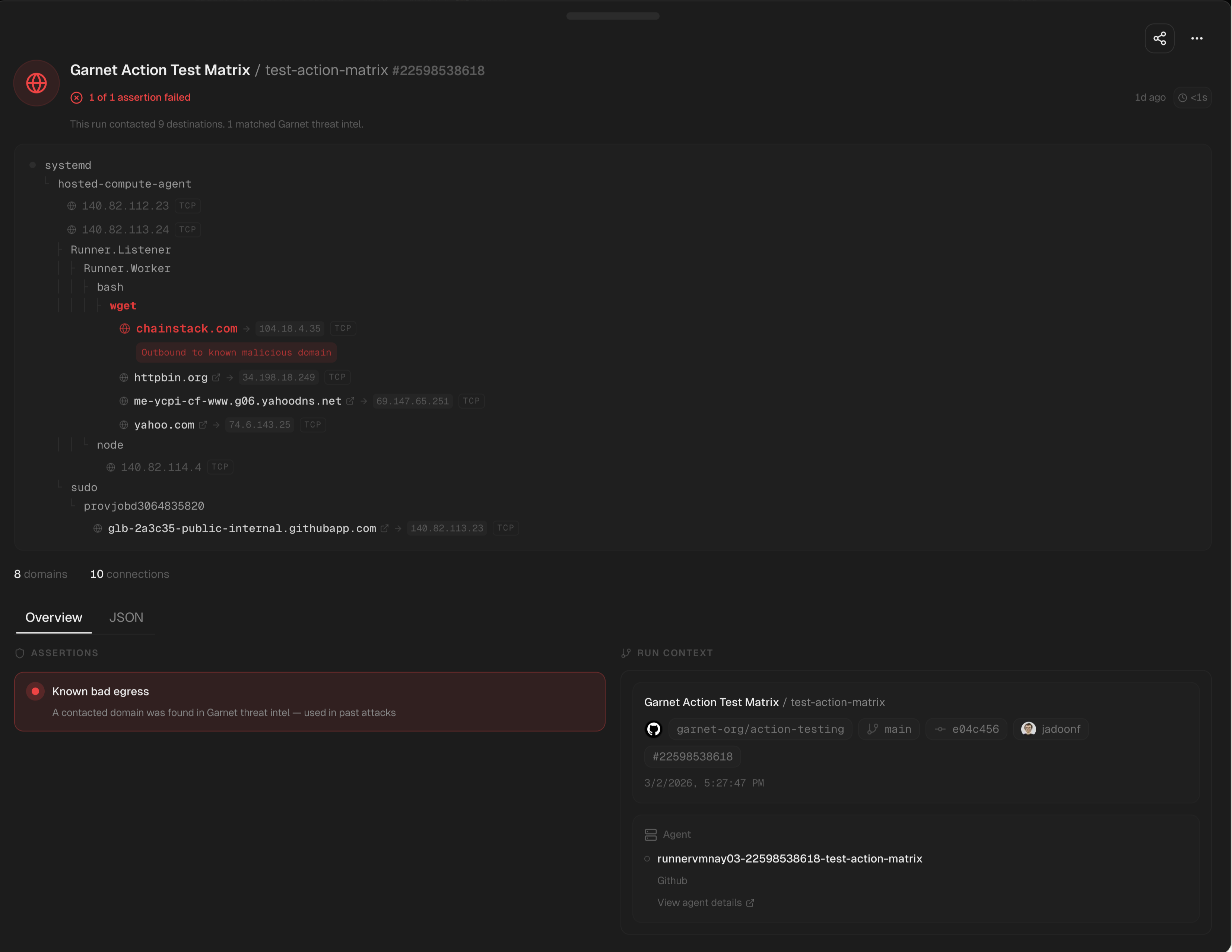
chainstack.com matched threat intel, traced to wget in the workflow. More write-ups →